Apache Rampart Developer Guide
Getting Involved in Rampart
Introduction
Components of Rampart- Rampart Core
- Rampart Policy
- Rampart Trust
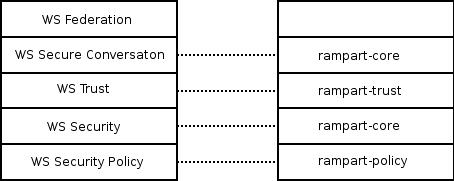
Figure 1 : Rampart Components and WS-Security Stack
Building Rampart
- Install maven3. Refer to the Installation guide.
- Download the source code.
- The Rampart project has 8 modules under it. They are:
- rampart-policy contains security policy assertions.
- rampart-core has core components that process and enforce security.
- rampart-trust contains trust components.
- rampart-mar builds the rampart.mar that is deployed in the "modules" directory of the Axis2 repository.
- rampart-trust-mar builds the rahas.mar that adds WS-Trust into Axis2.
- rampart-test has a set of unit test cases.
- integration-test has functional tests.
- rampart-samples consist of samples provided with the distribution.
- Build by typing
$mvn clean install
When deploying rampart.mar and rampart-trust.mar in the Axis2 repository, you may notice that they do not contain any dependencies. Therefore all the dependencies must be in the classpath.
Rampart in Axis2
Rampart is deployed as a module in Axis2, in the security phase. The security phase is right after the transport phase. The Rampart module introduces a couple of handlers - "org.apache.rampart.handler.RampartReciever" and "org.apache.rampart.handler.RampartSender" to the security phase.
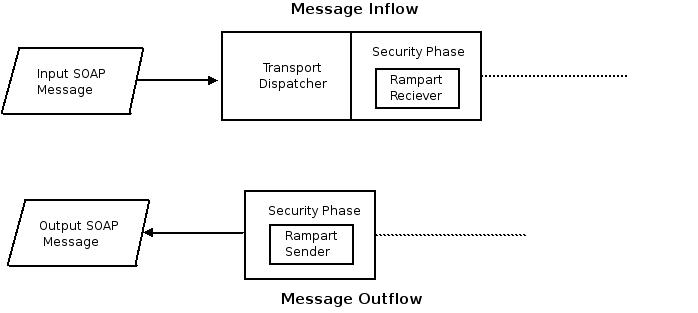
Figure 2 : Rampart in Axis2
The "RampartReceiver" handler intercepts the incoming message. Then Rampart validates the security of the incoming message, and checks whether it is in-line with the specified security policy. All security actions such as decryption of the message, validating the digital signature, validating the timestamp, and authenticating the user happens inside the Rampart module.
"RampartSender" is the last handler in the outflow. The outgoing message is intercepted by this handler and Rampart takes the security actions. For example SOAP message can be encrypted, digitally signed, and security tokens are included according to the security policy.
Rampart, WSS4J, and DOOM
Rampart uses WSS4J for securing SOAP messages. WSS4J is an Apache project which implements the WS-Security specification. SOAP messages are signed and encrypted according to the XML Encryption and XML Digital Signature specifications, but the WS-Security specification introduces an additional set of rules. Therefore WSS4J ensures that SOAP messages are singed according to all the rules defined in the specifications. WSS4J uses Apache's xmlsec libraries for XML Encryption and XML Digital Signature.
Rather than re-inventing the wheel, it was decided to use WSS4J for SOAP message security in Rampart but there was a fundamental problem. WSS4J and all the incorporating XML security libraries use "DOM" for parsing and generating XML, while Axis2 uses "AXIOM" as the object model. This was resolved by using a new object model named "DOOM". DOOM is both AXIOM and DOM implementations. Therefore you can manipulate/access a DOOM object structure through DOM interfaces and AXIOM interfaces.
When Rampart is engaged and configured, the incoming SOAP messages are converted to DOOM. Since DOOM implements the DOM interface it is possible for WSS4J to process messages. After performing the security validations, before flushing the message down the message inflow, the DOOM SOAP message is converted back to OM. At the outgoing flow, the message is converted to DOOM and then the security functions are performed using WSS4J.
Rampart Core
Rampart core drives security enforcement and validation on SOAP messages. It binds all components together to create the final product. The important components of Rampart core are,
- org.apache.rampart.RampartEngine
- org.apache.rampart.MessageBuilder
SOAP Message Inflow
Incoming messages are intercepted by RampartReciver and handed over to the RampartEngine. RampartEngine is responsible for handling validation of security in the incoming SOAP message.
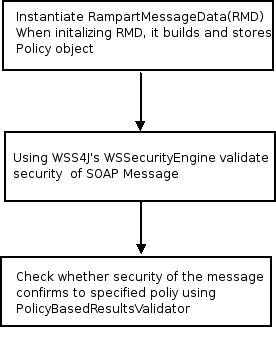
Figure 3: Control flow in RampartEngine
Note: RampartMessageData stores "org.apache.rampart.policy.RampartPolicyData", which contains security policy in the manner required by "RampartEngine" and "MessageBuilder".
SOAP Message Outflow
Outgoing messages are intercepted by RampartSender and handed over to org.apache.rampart.RampartMessageBuilder. It is responsible for enforcing security on an outgoing SOAP message.
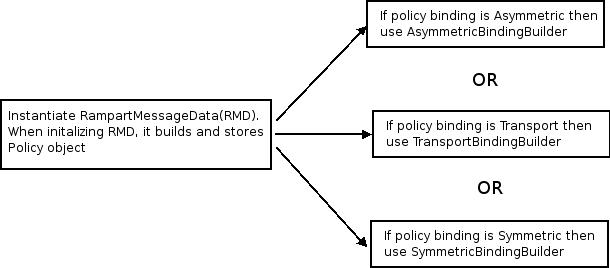
Figure 4: Control flow in MessageBuilder
Rampart Policy
WS - Security Policy is an extension of WS-Policy specification. Corresponding to this, the implementation of the security policy in Rampart is based on "Neethi", which is the Apache implementation of WS Policy specification. For each policy assertion introduced in the WS-Security Policy, there is an "Assertion Builder" and an "Assertion Model" defined in Rampart-policy.
Apache Neethi is a highly extensible framework. When reading a security policy file, these builders and models in Rampart Policy are picked up by the Neethi framework using the "Jar file Service Provider Mechanism". All Rampart builders are listed in the META-INF/services/org.apache.neethi.builders.AssertionBuilder file. When adding a new Policy assertion it requires only a builder, assertion model, and an entry in the file.
The RampartPolicyBuilder creates a RampartPolicyData given a "Policy" object created using the Rampart-policy and Neethi frameworks.
Rampart Trust
Rampart Trust implements the WS-Trust specification, which can be used in-conjunction with the Rampart Core and Rampart Policy modules. Rampart Trust defines a framework that can be used to issue, cancel, renew, and validate tokens, i.e., it defines a set of interfaces that must be implemented by different token issuing parties. Basically, Rampart Trust provides the functionality needed to host a STS - Security Token Service.
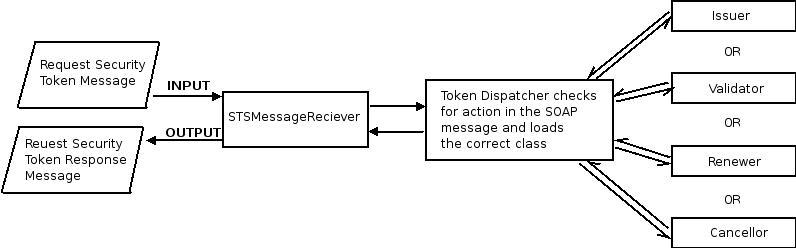
Figure 5: Control flow in Rampart Trust
Release process and release preparation
Check that all dependencies and plugins are available from standard repositories. To do this, clean the local repository and execute 'mvn clean install followed by 'mvn site'
Check that the set of license files in the legal directory is complete and accurate (by checking that in the binary distribution for every third party JAR in the lib directory.
Check that the apache-release profile (see the 'parent' reference in the top level pom.xml, and https://maven.apache.org/pom/asf/) can be executed properly. To do this, issue the following command: mvn clean install -Papache-release -DskipTests=true
You may also execute a dry run of the release process: mvn release:prepare -DdryRun=true. In a dry run, the generated zip files will still be labled as SNAPSHOT. After this, you need to clean up using the following command: mvn release:clean
Check that the Maven site can be generated and deployed successfully, and that it has the expected content.
To generate the entire documentation in one place, complete with working inter-module links, execute the site-deploy phase (and check the files under target/staging). A quick and reliable way of doing that is to use the following command: mvn -Dmaven.test.skip=true clean package site-deploy
Complete the release notes in the new src/site/markdown/release-notes .md file, i.e. 2.0.0.md. It should include a description of the major changes in the release as well as a list of resolved JIRA issues.
Prerequisites
The following things are required to perform the actual release:
A PGP key that conforms to the requirement for Apache release signing
To make the release process easier, the passphrase for the code signing key should be configured in ~/.m2/settings.xml
<settings>
...
<profiles>
<profile>
<id>apache-release</id>
<properties>
<gpg.passphrase><!-- KEY PASSPHRASE --></gpg.passphrase>
</properties>
</profile>
</profiles>
...
</settings>
The release process uses a Nexus staging repository. Every committer should have access to the corresponding staging profile in Nexus. To validate this, login to repository.apache.org and check that you can see the org.apache.axis staging profile. The credentials used to deploy to Nexus should be added to settings.xml
Release
In order to prepare the release artifacts for vote, execute the following steps:
If necessary, update the copyright date in the top level NOTICE file.
Start the release process with the following command - use 'mvn release:rollback' to undo:
mvn release:prepare
When asked for the "SCM release tag or label", keep the default value (x.y.z)
The above command will create a tag in Subversion and increment the version number of the trunk to the next development version. It will also create a release.properties file that will be used in the next step.
Perform the release using the following command:
mvn release:perform
This will upload the release artifacts to the Nexus staging repository.
Close the staging repository. The name of the staging profile is org.apache.axis. See for a more thorough description of this step.
Execute the target/checkout/etc/dist.py script to upload the source and binary distributions to the development area of the repository.
If not yet done, export your public key and append it here.
The command to export a public key is as follows:
gpg --armor --export key_id
Create a new staging area for the site:
svn copy https://svn.apache.org/repos/asf/axis/site/axis2/java/rampart https://svn.apache.org/repos/asf/axis/site/axis2/java/rampart-staging
This step can be skipped if the staging area has already been created earlier (e.g. to test a snapshot version of the site).
Change to the target/checkout directory and prepare the site using the following commands:
mvn site-deploy ; mvn scm-publish:publish-scm -Dscmpublish.skipCheckin=true
The staging area will be checked out to target/scmpublish-checkout (relative to target/checkout). Do a sanity check on the changes and then commit them.
Start the release vote by sending a mail to java-dev@axis.apache.org . The mail should mention the list of issues solved in the release (by linking to the relevant JIRA view).
Include a link to the location of the Nexus staging repository, and a link to the source and binary distributions.
A link to the preview of the Maven site.
If the vote passes, execute the following steps:
Promote the artifacts in the staging repository. See for detailed instructions for this step.
Publish the distributions:
svn mv https://dist.apache.org/repos/dist/dev/axis/axis2/java/rampart/ https://dist.apache.org/repos/dist/release/axis/axis2/java/rampart
Publish the site:
svn co --depth=immediates https://svn.apache.org/repos/asf/axis/site/ site ; cd site/axis2/java ; svn rm rampart ; svn mv rampart-staging rampart ; svn commit
It may take several hours before all the updates have been synchronized to the relevant ASF systems. Before proceeding, check that the Maven artifacts for the release are available from the Maven central repository, and the Rampart Maven site has been synchronized.
Verify the binary and source distributions can be downloaded from the Rampart download page.
Once everything is in place, send announcements to java-dev@axis.apache.org and announce@apache.org. Since the two lists have different conventions, audiences and moderation policies, to send the announcement separately to the two lists.
Sample announcement:
Apache Rampart Team is pleased to announce the release of Rampart x.y.z. The release is available for download at:
https://axis.apache.org/axis2/java/rampart/download.html
Apache Rampart provides implementations of the WS-Sec* specifications for Apache Axis2, based on Apache WSS4J and the Apache Axiom DOOM implementation.


